SAP Security Notes September ‘19: Critical Solution Manager Patch Now Available for Windows
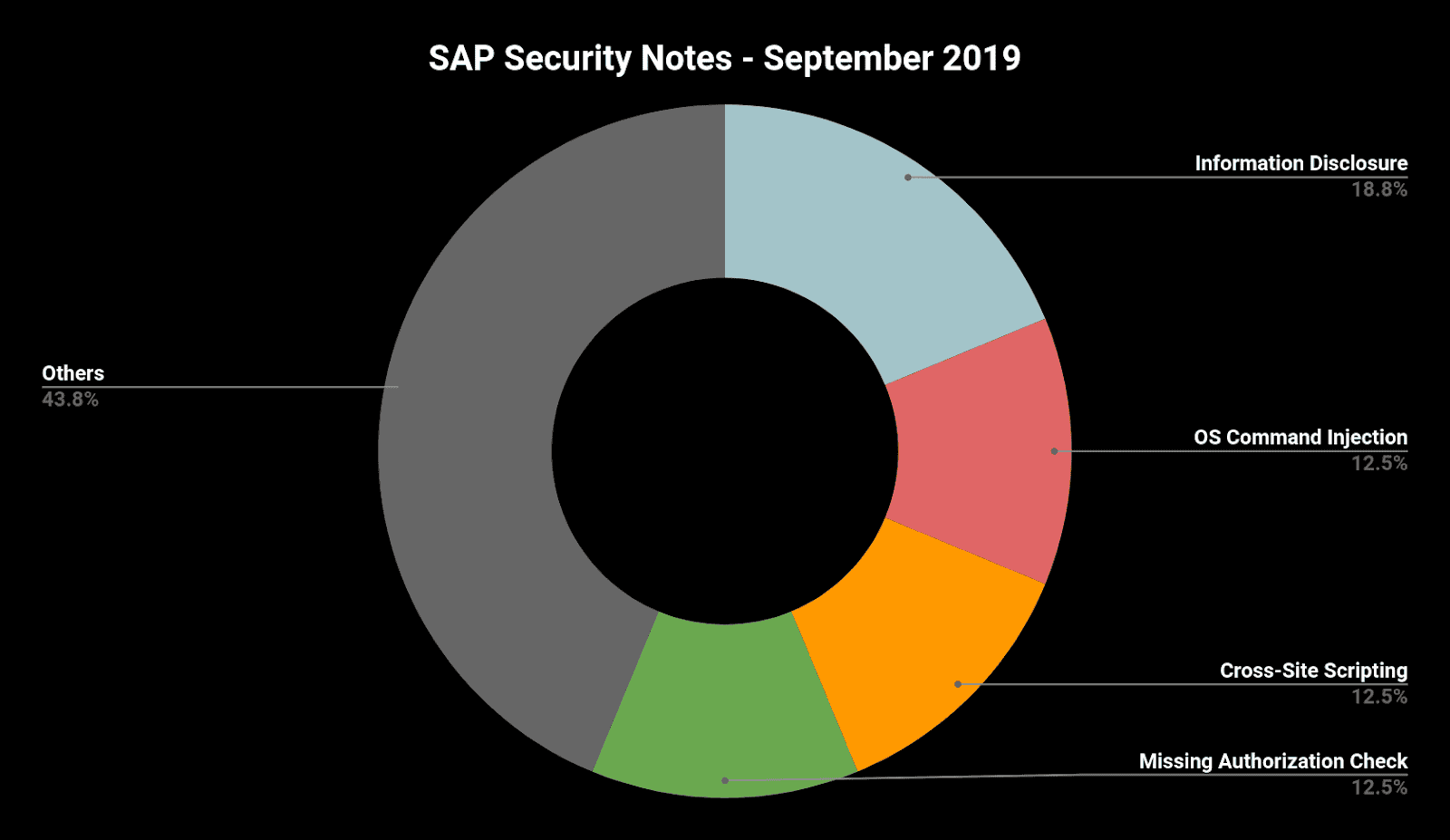
Highlights of September’s SAP Security Notes analysis include:
- Critical vulnerability in Solution Manager Diagnostics Agent now also fixed for Windows—New HotNews issued based on feedback from the Onapsis Research Labs regarding the initial published note
- Multiple vulnerabilities fixed in SAP HANA Extended Application Services—Denial of Service vulnerability reported by Onapsis Research Labs leads to extensive corrections for SAP HANA XSA
- SAP NetWeaver AS for Java components affected above-average—Five of sixteen notes related to Java stack
Today, SAP published its monthly Security Notes for September 2019. We are proud to announce that two of our reported vulnerabilities resulted in fixes that are now available for all SAP customers, furthering our joint effort to make SAP systems more secure. Two of the HotNews Notes, #2808158 and #2823733, both address our reported Diagnostics Agent vulnerability. This demonstrates that our Research Labs is not only looking for new vulnerabilities but are also checking the results of already published fixes to detect any gaps in the provided solution.
A detailed analysis of the four HotNews notes shows that the only really new one is SAP Security Note #2798336 “Code Injection Vulnerability in SAP NetWeaver AS for Java (Web Container).” HotNews Note #2622660 is just another update on the Google Chromium control delivered with SAP Business Client that was published between the current and the last patch day.
The only High Priority note, #2817491 titled, “Multiple Security Vulnerabilities in SAP HANA Extended Application Services (Advanced Model),” fixes a Denial of Service as well as an Internal Port Scanning vulnerability, both reported by Onapsis.
HotNews SAP Note in Solution Manager Diagnostic Agent Now Fixed in Windows
Two months ago, SAP released a critical vulnerability affecting Solution Manager (SolMan) that was discovered by the Onapsis Research Labs and was already explained in our July SAP Notes blog post. After its release, our team analyzed the patch and discovered that it was only fixed for SAP systems in Linux, and was not for Windows systems, which was again properly reported. Today, SAP fixed this by publishing SAP Security Note #2823733, “Update 1 to Security Note #2808158: [CVE-2019-0330] OS Command Injection vulnerability in SAP Diagnostics Agent,” which is also a HotNews due to its criticality and its low attack complexity (CVSS score of 9.1). A SolMan admin can abuse the Diagnostic Agent (SMDAgent) bug and gain access to any SAP system connected to the SolMan system.
Even though many SolMan admins have admin privileges in other SAP systems, certain scenarios may allow an escalation of privileges to those who don’t. This is especially true in bigger companies where the SAP landscape is broad and certain users may not have privileged access to every system, because of job responsibility, geographic location or other business reasons. This escalation privileges scenario is especially valid for companies that have contractors, whose access is usually more focused on the specific systems they are authorized to access.
If these scenarios pertain to you, increasing the urgency to patch should be a priority since it may be one of the most critical ones patched by SAP so far in 2019. While installing critical patches should always be a priority, this bug can affect the entire landscape, especially considering SMDAgent is installed in every SAP system (for diagnostic tasks).
Even if you already installed the original note released in July (#2808158), you should also install SAP Security Note #2823733. On the other hand, if you did not install the old note, you can directly proceed and install the new one.
SAP HANA XSA Login Vulnerable to Denial Of Service
The SAP HANA XS User Account and Authentication service (UAA) is the central infrastructure component of XS Advanced model for user authentication. The UAA uses OAuth 2.0 and provides a user authentication interface that could be accessed from external applications, and once the user has been validated, it is redirected to the application that is requesting access.
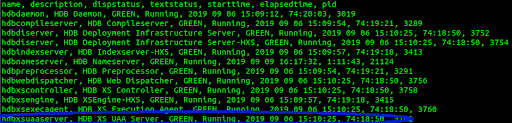
This component is part of the XS Advance platform by default and it is possible to verify if the component is running by executing the sapcontrol -nr NN -function GetProcessList command. Doing this will show different services, with one of them being the hdbxsuaaserver, HDB XS UAA Server. Alternatively, you can directly access https://<host>:30032/uaa-security-oidc/login, which is the default port and path of the web service, to see if it’s configured by port.
If you have the component enabled (which should be the case if you are an SAP HANA XSA user), you are vulnerable to the High Priority note released by SAP today: #2817491 “Multiple security vulnerabilities in SAP HANA Extended Application Services (Advanced Model).” This note fixes two different bugs reported by Onapsis researchers, where the most critical one allows an authenticated attacker to cause a Denial of Service exploitation, simply by providing a specially crafted payload several times to an endpoint of the XS Advance UAA component, depleting the database connections and consequently preventing the legitimate use of the service.
Taking into consideration that this service is necessary to authenticate other XS Advance web services, and there may be users created in applications that take advantage of this feature, this attack could lead to some customer developed applications also being inaccessible due to the lack of this authentication provider.
Further HotNews SAP Note Addressing a Code Injection Vulnerability in SAP NetWeaver AS for Java
SAP Note #2798336 “Code Injection Vulnerability in SAP NetWeaver AS for Java (Web Container)” with a CVSS rating of 9.1 fixes a program error in the SAP default implementation of the HTTP PUT method that allows attackers to bypass the input validation check. Without a validation check, an attacker is able to upload dynamic web content and thus can take control of the whole application. Possible impacts are:
- Unauthorized execution of commands
- Sensitive information disclosure
- Denial of Service
We strongly recommend that you apply the corresponding Support Packages and Patches as the exploitation of the vulnerability is not very complex and does not require high privileges. Taking into account the wide range of possible impacts, this vulnerability represents a very attractive target for any attacker.
Summary & Conclusions
With 16 new or updated Security Notes released today, the number of published Security Notes is lower than in August. However, some of them include multiple fixes or important updates and extensions to already published notes and thus reminding us that patching is and will remain a continuous major task for every SAP customer. The Onapsis Platform can help reduce the burden of patching by running the Missing Notes Module to simplify vulnerability and compliance checks and prioritize your patch process based on criticality and business impact.
Our researchers, Ignacio Favro, Pablo Artuso and Yvan Genuer were credited by SAP in its acknowledgment webpage for our collaboration this month. The Research Labs is already working to update the Onapsis Platform to incorporate these newly published vulnerabilities into the product so that our customers can check missing notes during their security assessments.
For more information about the latest SAP security issues as we continue with our efforts to share knowledge with the security community, subscribe to our monthly Defender’s Digest Newsletter and remember to register for our live webinar on Sept 17th for an overview of the highlights from this month’s security notes, steps for a successful and efficient patch and live Q&A with the Onapsis Research Labs.
