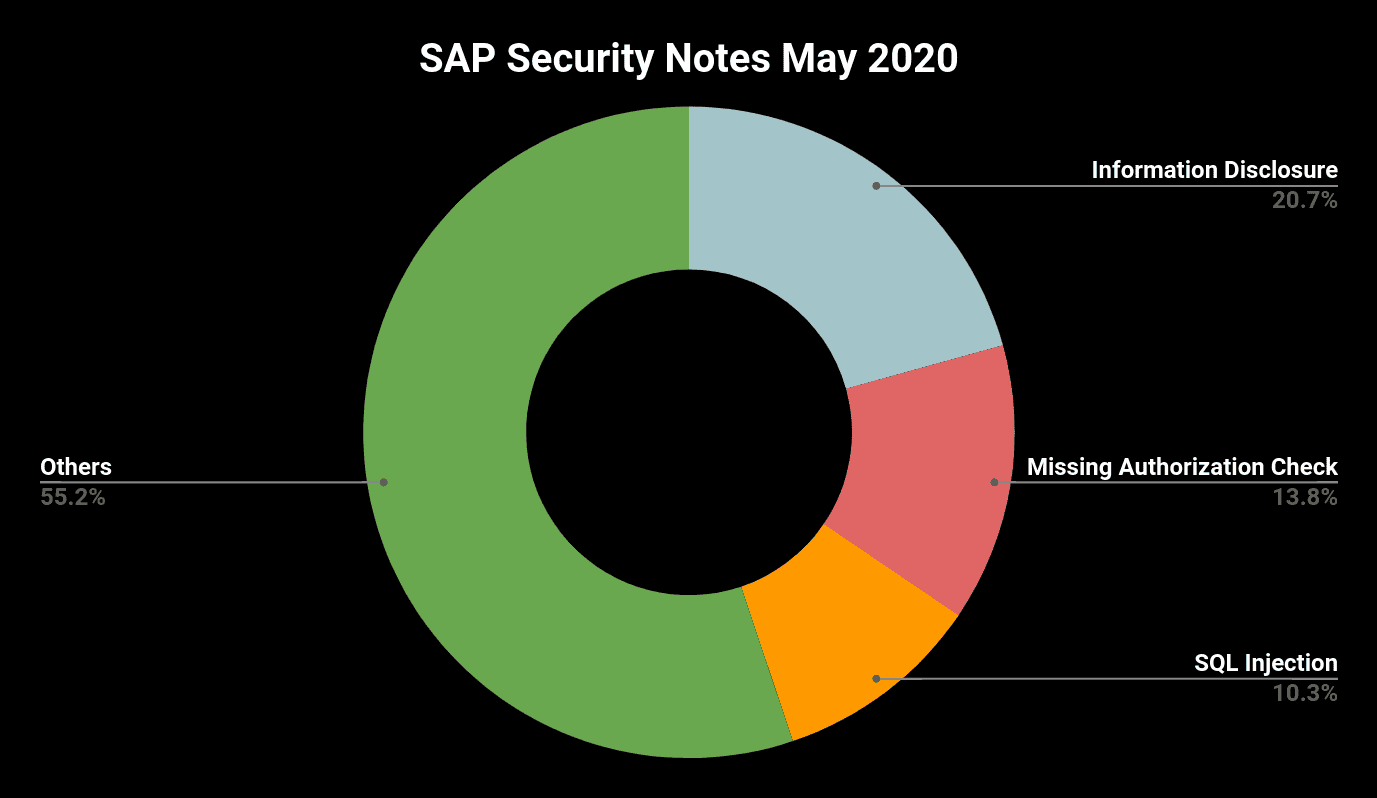
SAP Security Patches May 2020: Second Month in a Row with 29 Total Fixes Released
Highlights of May SAP Security Notes analysis include:
- May summary—29 new and updated SAP security patches released including six HotNews Notes and seven High Priority Notes
- SAP ASE affected most—SAP Adaptive Server Enterprise with five critical fixes and seven fixes in total
- Onapsis Research Labs Collaboration—Our team helped SAP fix a Medium Priority note with a potential Denial Of Service vulnerability
For the second month in a row, SAP released 29 fixes on its regular patch day, a bigger number than any average month in the last year. While the number of total fixes has been stabilized at a relatively high level, the amount of critical patches has increased. Facing six HotNews notes and seven High Priority notes, there are a lot of patch activities required for SAP customers this month. However, a more detailed analysis reveals at least five of the critical patches only affect customers running SAP on SAP Adaptive Server Enterprise (SAP ASE).
In Focus of May’s Patch Day: SAP Adaptive Server Enterprise (SAP ASE)
SAP’s May Patch Day includes a large number of fixes for SAP ASE. SAP ASE is one of the SQL database servers supported by SAP business applications. It uses a relational data management model and provides on-premises as well as cloud deployment options.
The detected issues comprise different types of vulnerabilities. The most critical ones, based on CVSS score, are the two HotNews notes #2917275 and #2917090. While the first note fixes a Code Injection vulnerability in the Backup Server of SAP ASE, the second note solves an Information Disclosure vulnerability in the SAP ASE Cockpit. The respective CVSS of 9.1 and 9.0 reflect the criticality of these vulnerabilities.
Also included are three High Priority notes being released for SAP ASE. SAP Security Notes #2916927 and #2917273 fix SQL Injection vulnerabilities that can lead to an escalation of privileges and thus allowing authenticated users to execute commands that they are otherwise not allowed to execute. Compared to the CVSS of 8.8 for the vulnerability described in the first note, the CVSS of the second one is somewhat lower as an attacker needs more authorizations to exploit it. The third High Priority note for SAP ASE, SAP Security Note #2915585 with a CVSS of 8.0, describes a vulnerability found in the XP Server component and only affects installations on Windows platforms. The vulnerability allows the injection of code and enables an attacker to read, modify or delete restricted data.
Other Notable Critical SAP Security Notes in May
The most critical note is HotNews note #2835979 with a CVSS of 9.9. Due to an insufficient input validation in a remote-enabled function module that dynamically generates code, an attacker can take complete control of any SAP NW ABAP system that is connected to a Solution Manager (SolMan) system. Only the fact that an attacker needs a minimum level of authorizations to exploit this vulnerability has prevented it from receiving a CVSS of 10.0. Fortunately, there are no manual steps involved in the provided fix. Onapsis recommends applying the corresponding patch as soon as possible!
Two HotNews notes affect SAP BusinessObjects Business Intelligence platform. SAP Security Note #2885244 describes a scenario that leads to a missing authentication vulnerability. Thanks to the unchanged scope in case of an exploit, the CVSS is “only” 9.8. HotNews note #2863731 titled, “Deserialization of Untrusted Data in SAP Business Objects Business Intelligence Platform (CR .Net SDK WebForm Viewer)” and scored with CVSS of 9.1, contains updates on a vulnerability in SAP BusinessObjects that was initially published on April’s Patch Day.
The set of six HotNews notes is completed by another update of SAP Security Note #2622660, providing a new patch level for SAP Business Client. These patches provide support for Chromium version 81.0.4044.92. Details about the concrete fixes that are shipped with this Chromium version can be found here.
Further High Priority notes in descending order based on CVSS score include:
|
SAP Security Note |
Affected Component |
Vulnerability |
CVSS |
|
SAP Landscape Management |
Information Disclosure |
8.7 | |
|
SAP Master Data Governance |
SQL Injection |
7.7 | |
|
SAP ABAP Server |
Information Disclosure |
7.4 | |
|
SAP Business Client |
Binary Planting |
7.0 |
Cross-Site Scripting Vulnerability in SAP Enterprise Threat Detection Fixed
The most important aspect of any security measure is that it does not introduce any additional vulnerabilities to a customer’s environment. SAP has therefore fixed a CVSS of 6.1 vulnerability in SAP Enterprise Threat Detection (ETD). SAP Security Note #2913293, an insufficient encoding of specific pages, exposed a Cross-Site Scripting vulnerability with the following potential impacts:
- Non-permanently deface or modify displayed content from a website
- Steal authentication information of the user, such as data relating to his or her current session
- Impersonate the user and access all information with the same rights as the target user
These impacts demonstrate that it is not enough to establish appropriate security measures for an IT infrastructure, but it is at least as important to protect these measures themselves. SAP is aware of this philosophy and uses a lot of effort, together with security researchers all over the world, to protect its customers. Nevertheless, it also needs customers’ collaboration. This includes the implementation of specific security guidelines, periodic patching and monitoring as well as continuous fine-tuning of security measures. Refer to the Onapsis blog post Securing Your SAP and Securing the Security of Your SAP to see best practices for keeping security settings in SAP secure.
Summary & Conclusions
As most of our readers may know, the Onapsis Research Labs is continuously looking for vulnerabilities in mission-critical applications and works closely with SAP to help its security team fix the bugs as soon as possible. This month, we also collaborated with the report about a Denial Of Service (DoS) vulnerability patched in SAP Security Note #2856923 [CVE-2020-6240], which fixes a DOS vulnerability in SAP NetWeaver Application Server ABAP (Web Dynpro ABAP).
Finally, here’s a summary of May’s SAP Patch Day:
- The number of critical fixes, as well as the total number of fixes, remains high
- SAP SolMan remains an attractive target for attacking arbitrary SAP systems
- Components that were not that visible on former patch days received a lot of attention (SAP ASE)
As always, the Onapsis Research Labs is already updating The Onapsis Platform to incorporate the newly published vulnerabilities into the product so that our customers can protect their businesses.
For more information about the latest SAP security issues and our continuous efforts to share knowledge with the security community, subscribe to our monthly Defender’s Digest Onapsis Newsletter.