Alex Horan
Alex Horan is the Vice President of Product Management for Onapsis, where he focuses on developing solutions for SAP security and ERP vulnerability management. With over 18 years of experience, Alex has a proven track record of helping large companies enhance their security posture. His expertise spans key areas such as vulnerability assessment, penetration testing, and systems auditing, making him a trusted voice on topics like SAP compliance and secure system configuration. He is committed to ensuring that Onapsis’s products provide advanced protection against real-world threats like ransomware and unauthorized access.
AppsMas: Onapsis Platform 2022 Highlights
Let’s take a look at 2022 and see what key Onapsis Platform enhancements launched throughout 2022.
Fact or Fiction: Business-Critical Application Security Edition
As business-critical application security experts (SAP, SFDC, Oracle) we know the many tales and misconceptions surrounding the current threat landscape. Let’s take a look at some common misconceptions around business-critical application security and use these insights to help make better decisions to keep your organization secure.

Security Guy TV Interview
Onapsis Director of Product Management, Alex Horan, had the pleasure of speaking with Security Guy TV host, Chuck Harold, at Black Hat Las Vegas 2019 earlier this month.
GDPR is Not Just About Customers, But Employees Too
GDPR is finally here. You’ve thought of everything, except how to handle your employees’ user information…

How The Newly Released OWASP Top 10 Affects Your SAP Systems
After much review, and various release candidates, OWASP has released their new Top 10 that reflects what are generally considered to be the most critical security risks to web applications.
How the Proposed OWASP TOP 10 Changes Would Affect SAP and Oracle
While only in release candidate form, the current proposed changes to the OWASP Top 10 Application Security Risks provide clear guidance for any enterprise that needs to secure and protect their critical enterprise business applications. In general, the OWASP Top 10 and these two additions can be directly applied to an approach and methodology for securing ERP…
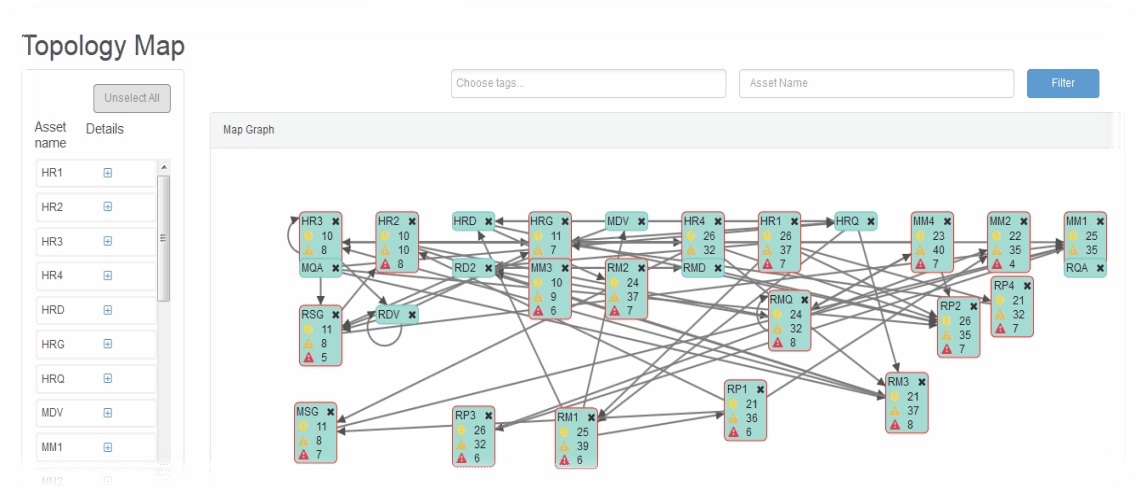
Now Announcing: Splunk Integration with OSP!
As the Onapsis Security Platform continues to become more widely adopted throughout global enterprises, we have received an overwhelming number of requests to integrate OSP with our customer’s existing SIEM solutions. Based on these requests, we are excited to announce that we have officially launched an integration with Splunk Enterprise. This marks our second SIEM…
