Analyzing SAP Security Notes February 2016
SAP is a complex and ever changing system, whether because of changes introduced to your SAP implementation to better suit your business or through the application of Security Notes (Patches) to ensure that newly disclosed vulnerabilities are mitigated.
In order to provide a predictable and scheduled flow of vulnerability mitigation information and security patches, SAP releases the major part of their latest Security Notes information on the second Tuesday of every month. Due to this regular disclosure of new security issues that could potentially weaken the security of SAP systems within an organization, it’s highly recommended to carry out periodic assessments on a monthly basis at least.
At Onapsis we are very concerned about our client’s SAP system security and also the state of SAP security in general, so to assist our customers, we perform a detailed analysis of the monthly SAP Security Notes as soon as they are published. The goal of this is to provide SAP clients with detailed information about the newly released notes and vulnerabilities affecting their SAP systems and help guide their testing of these systems within their organization.
Between the last published SAP Security Tuesday and today, there were 23 SAP Security notes published by SAP AG (taking into account 7 Support Packages and 16 Patch Day Notes). The Onapsis Research Labs contributed as almost every month, on reporting vulnerabilities found in the SAP Software (Acknowledgments to Security Researchers).
The SAP Security Notes released this month, related to advisories reported by the Onapsis Research Labs were:
- 2252312; 1.7 (AV:L/AC:L/Au:S/C:N/I:P/A:N). Insufficient logging of RFC in SAL
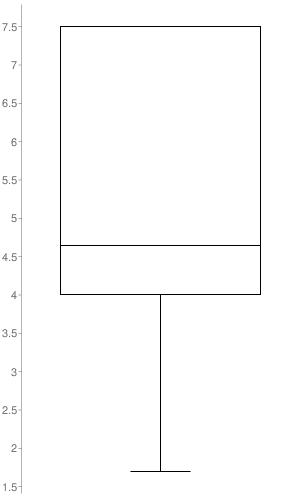
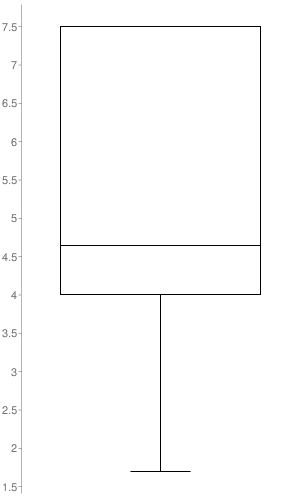
The box-plot graph illustrates the distribution of CVSS v2 scores across the Security Notes released. The only notes taken into account to build it, were the ones to which SAP set a CVSS v2 (16 out of the 23 SAP Security Notes). As it’s represented in the graph, the SAP Security Notes range values go from 1.7 to 7.5 with a median of 4.6.
SAP Security Notes with higher CVSS scoring provided by SAP
- 2234226 – 7.5 (AV:N/AC:L/Au:N/C:P/I:P/A:P). TREX / BWA: Potential technical information disclosure / host OS compromise. This SAP Security Note has been updated in note 2273881. There is an interface in TREX / BWA that lets an unauthenticated user to execute OS commands using SIDadm permissions on the machine that runs the TREX / BWA application.
- 2101079 – 6.8 (AV:N/AC:M/Au:N/C:P/I:P/A:P). Potential modif./disclosure of persisted data in BC-ESI-UDDI. There was a security issue in the component “UDDI Server” which would allow a malicious user to send customized inputs to an SAP System and retrieve, modify or delete data persisted in it.
- 2256846 – 5.0 (AV:N/AC:L/Au:N/C:P/I:N/A:N). Potential information disclosure relating to usernames. The Universal Worklist (UWL) provides users with the People Picker functionality, this feature had a vulnerability which could allow an attacker to retrieve information about usernames with permissions to use it.
Other corrections with High Priority (no CVSS provided by SAP)
- 2262104. Security vulnerabilities found in Apache Commons Collections library used in CA Introscope.
- 2273881. Update 1 to Security Note 2234226.
- 2268810. Security vulnerability in Apache Commons Collections library used by multiple SAP Lumira products.
- 2246851. PI SEC: Security vulnerabilities found in Apache Commons Collections library used in Enterprise Services Repository.
- These four SAP Security Notes are related to the vulnerability found in Apache Commons Collections library.
- 2245130. Potential bypass of unified connectivity runtime checks possible in BC-MID-RFC. In case the first user logon failed, it was possible to bypass the Unified Connectivity checking.
- 2177403. Missing authorization check in IS-A-VMS. The component Vehicle Management System had a vulnerability that would let an authenticated user to execute a particular Function to which access should be restricted.
- 2180125. Missing authorization check in LE-TRM. The component Task & Resource Management wasn’t correctly validating access to some of its functions, allowing an authenticated user to use certain functions to which access should be restricted.
Other attack vectors
- Reflected Cross-site Scripting (XSS): Notes 2249364, 2272211, 2220571, 1865646
- Stored Cross-site Scripting (XSS): Note 2228405
- Missing authorization check: Notes 2236289, 2214442, 2258608
- Insufficient Audit Logging: Note 2252312
- Denial of Service: Note 2266565
- Directory Traversal: Notes 2235088, 2230978
- XML External Entity (XXE): Note 2244346
Each month Onapsis updates its flagship product Onapsis Security Platform (OSP) to allow you to check whether your systems are up to date with these latest SAP Security Notes as well as ensuring those systems are configured with the appropriate level of security to meet your audit and compliance requirements.
Stay tuned for next month’s Security Notes analysis from the Onapsis Research Labs.
NOTE:
SAP published their monthly post in their SCN space “The Official SAP Product Security Response Space”, providing information about the SAP Security Notes.
Here it’s the link to the SAP blogpost: “SAP Security Patch Day – February 2016”

