SAP Security Notes August ‘18: SQL Injection in BusinessObjects and Several High Priority Notes to take care of.

Today is the second Tuesday of the month, meaning SAP has published a new batch of security notes to patch vulnerabilities found in its software. Below is our monthly analysis regarding SAP vulnerabilities fixed, to help keep your ERP environment safe and protected.
From the last patch Tuesday, a total of 27 new notes were published. Today, 15 of those notes were posted. There are no new notes tagged as Hot News, but don’t get too comfortable since there is still a need for action: nine notes were reported as High Priority. Two of these High Priority notes concern vulnerabilities reported by Onapsis Research Labs: one fixes two SQL Injection vulnerabilities in SAP BusinessObjects. Basically, an attacker with a low privileges session can inject data and extract information that he should not be able to. The other vulnerability fixes two bugs found in SAP HANA XSA. This month too, SAP has published and confirmed a vulnerability found during our concentrated research efforts on HANA XSA: users that were able to get a token before getting blocked/deleted or suffering an authorization change, will still be able perform the same actions he was able to perform before, as long as the tokens don’t expire.
In the following sections we will further explain both vulnerabilities.
All remaining notes this month are of Medium Priority, 18 to be precise; we do not see any Low Priority notes appearing this time.
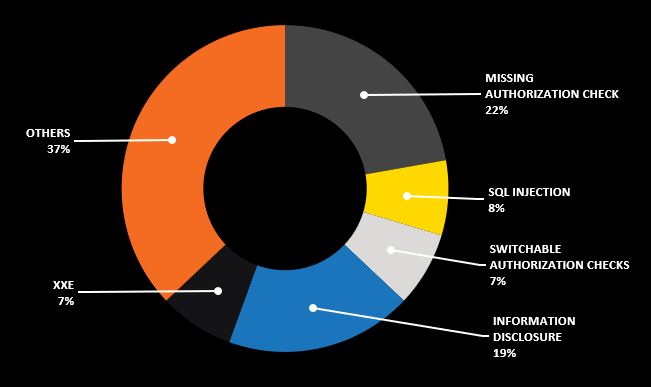
This month the types of vulnerabilities reported are a mixed bag, affecting several products in a range of different ways. For instance, we see High Priority notes concerning SQL Injection, missing authorization check, information disclosure and even XSS in products like SAP Crystal Reports, SAP Financial Consolidation and SAP Environment, Health and Safety (EHS). More about those High Priority notes later in this post.
Below is a chart showing this month’s notes vulnerability category distribution:
Fixes for Onapsis reported BusinessObjects and SAP HANA XSA
As you may already know, the Onapsis Research Labs has been putting special focus on SAP HANA and, more recently, on the SAP BusinessObjects platforms. Two SAP Security Notes from this month are fix a couple of security issues found by our Lab’s researchers on each of these two platforms.
SAP Security Note #2590705 fixes two bugs found by Onapsis researcher Pablo Artuso in SAP HANA XSA with the implementation of the OAuth2 authorization mechanism by means of JSON Web Token (JWT). One of the problems fixed has to do with the validity of the token.
If captured by an attacker, the token allows him/her to access resources with the same authorizations of the abused user for a long period of time, for up to 12 hours. This is possible even if the user has ended its session.
The other problem with this “long lasting” token is that even after an administrator has revoked permission to a user, its token is still valid and still contains the valid permissions at the time the token was issued. This allows some problematic scenarios.
For example, if an administrator restricts a user’s permissions and the user has a valid session at that moment, that change will not be in effect until the token’s lifetime expires, probably after several hours thus allowing the user system access as if nothing changed. Another possible scenario could be when a user is deleted by the administrator while the user is still logged. Its token allows keeping access to the system without changes.
This may represent a serious delay for some user management changes. But if we consider the scenario of a session token captured by an attacker that managed to get that token, this allows a long time window to abuse the system.
The SAP BI BusinessObjects Enterprise (BOBJ) platform is managed through a web-based application called Central Management Console (CMC). This console resides in the Central Management Server (CMS) that stores in its own System Database, all the configuration data including users, folders, access rights, SSO, services and other management data.
Another High Priority Note reported by the Onapsis Research Labs, #2644154, is tagged with a CVSS v3 base score: 7.7/10. It fixes two SQL-injection (SQLi) vulnerabilities found in SAP BusinessObjects (BOBJ) by Onapsis researcher Gaston Traberg. The issues were found in the frontend webserver of the Central Management Console (CMC). One of these SQLi is a blind boolean-based SQLi, and the other a regular SQLi vulnerability.
The difference between SQLi and blind SQLi is that the blind one is used to ask only for true or false to the database, because the exposed application retrieves only generic messages. The SLQi is still there and can be exploited, requiring more effort to the attacker.
These SQLi vulnerabilities, now fixed in the BOBJ’s CMC and reported by Onapsis, allow an attacker without privileges to get information from the Central Management Server System Database. As described, it is sensitive infrastructure information related to the BusinessObjects Enterprise platform, its structure and configuration.
No Hot News, High Priority Notes Released This Month
Below, this month’s remaining eight High Priority notes are discussed:
- XML External Entity Vulnerability in Crystal Reports for Enterprise (#2569748) – This note addresses a vulnerability in the Crystal Reports for Enterprise, a component of the BusinessObjects Enterprise platform. The vulnerability allows crafted XML content into an Xcelsius SWF object to cause a crash or hang when users interact with it when embedded into a Crystal Report.
- Missing Authentication Check in SAP SRM MDM Catalog (#2655250) – A function for catalog importing in SAP SRM, lacks the authentication for a proper repository user. That security bug allows unauthenticated users to access internal information.
- Memory Corruption Vulnerability in SAP BusinessObjects Business Intelligence Platform (#2614229) – This note resolves a vulnerability in a third-party software included in SAP BusinessObjects BI platform. Onapsis’s researcher Waldo Spek discussed this in the blog, The Risks of Open Source, some months ago. In this case it is the third-party open source Google Protobuf which provides methods to serialize structured data. The case is such that an attacker can take advantage of the vulnerability to cause memory corruption. This generally opens a way for the attacker to abuse the system with a code execution, or other abuses. This bug requires the installation of the appropriate support package patches. Note that this vulnerability does not affect 32 software versions.
- Cross-Site Scripting (XSS) Vulnerability in SAP Financial Consolidation (#2621395) – The SAP Financial Consolidation platform is a member of the SAP BusinessObjects Platform related solutions. This security issue, fixed with this note, is one that allows the user to abuse the poorly encoded user managed data that may result in a Cross-Site Scripting (XSS). The common risk of an XSS applies in this scenario, like stealing user authentication information and impersonating the user. To fix the issue the proper patch has to be installed.
- SQL Injection Vulnerability in SAP MaxDB/liveCache (#2660005) – This is a security issue with the SAP live cache technology in MaxDB versions 7.8 and 7.9. It allows an attacker to get the DBM operator privileges and abuse them to, at the end, read, modify or delete sensitive information from the database. The required update of the software solves the problem by removing those abusable privileges from the DBM operator.
- Missing Authorization Check in SD-SLS, SD-CAS and SD-MD-AM-CMI (#2155614) – This High Priority note fixes the lack of authorization checks in three SD components: Sales (SD-SLS), Computer-Aided Selling (SD-CAS) and Customer Material Information (SD-MD-AM-CMI). The absence of authorization checks is in three reports accessing Customer Master Data and General Material Data, so a user or an attacker can take advantage of this when it is missing to read or modify data without the necessary authorization. It is curious because the newly released version shows no difference with its previous two iterations from 2015. Not only is the text exactly the same, but the Service Packages are not new ones, neither the corrections instructions. It looks like a mistake. No need to re-install.
- Potential Information Ddisclosure Relating to Retrieve Safety Information (#2016974) and Inspect Safety Controls (#2017041) – These other two High Priority notes are to fix the SAP Environment, Health and Safety Management (EHSM) that is an add-on to SAP ERP. Both notes fix a potential information disclosure due to a browser cache stored information. Both Security Notes are new, but interestingly the security patch fixing the issue was issued in October 2014.
In the last three High Priority notes described above, we have seen with certain surprise that SAP is releasing the corresponding Security Note after a period as long as four years after the service package that corrects the bug was available.
Conclusion
We are in the process of updating the Onapsis Security Platform to incorporate these newly published vulnerabilities. This will allow our customers to check whether their systems are up to date with the latest SAP Security Notes and will ensure that those systems are configured with the appropriate level of security to meet their audit and compliance requirements. Please check our website for additional information on all topics discussed in this blog post.